OT Network Security for Oil & Gas
Owl’s hardware-enforced protocol filtering diode ensures safety, speed, and simplified compliance.
Get Started
Prevent Pipeline Disruptions
The oil and gas industry faces a constant cyber security challenge: keeping Operational Technology (OT) networks secure while maintaining visibility across upstream, midstream, and downstream operations. As ransomware and targeted attacks grow more sophisticated, traditional, software‑only defenses can either leave gaps or force “abundance of caution” shutdowns that halt product flow.
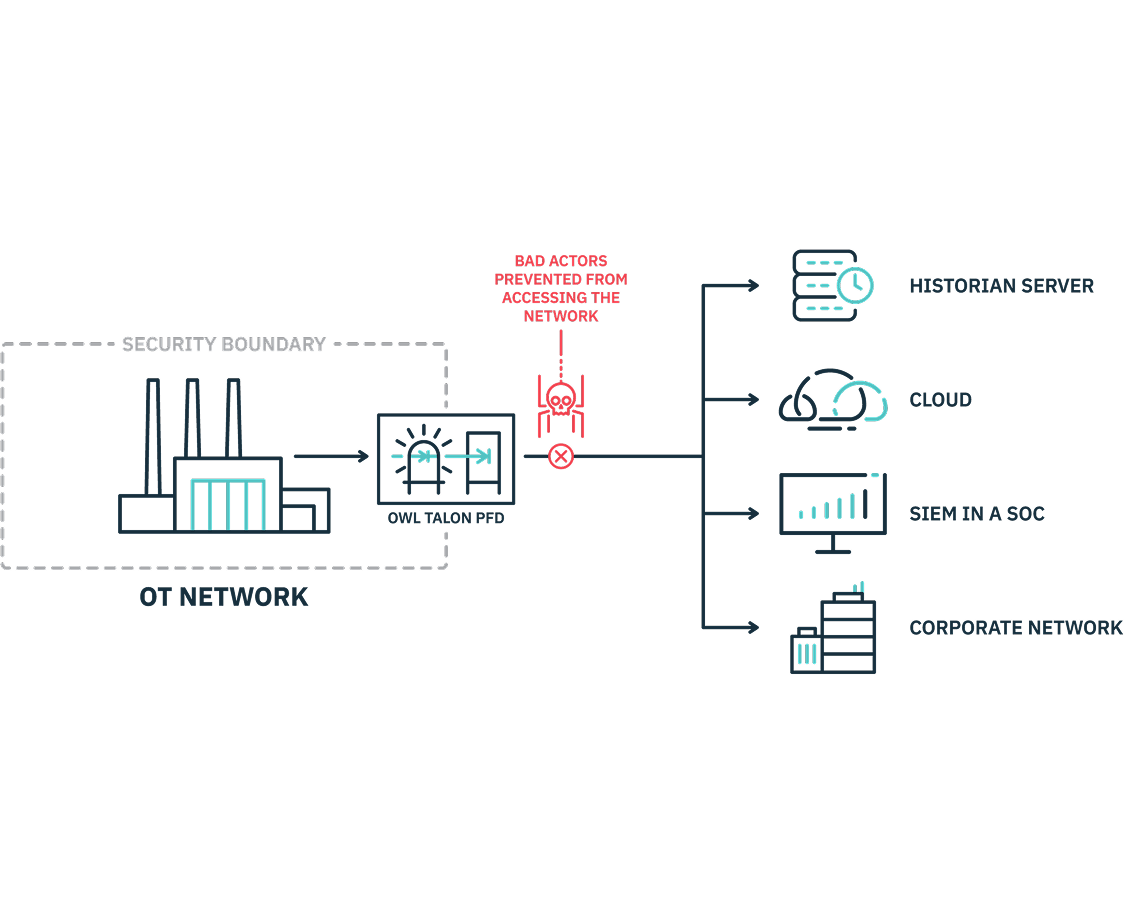
Owl Cyber Defense addresses this with hardware‑enforced data diodes that let you safely move pipeline and SCADA data one way out of OT networks to IT, historians, SIEM platforms, and the cloud—without creating a path back in. Your OT environment stays segmented, monitored, and resilient, so pipelines keep running and critical data stays protected from external threats.
Securely Transfer Data To Those Who Need It
Hardware-enforced data diodes give oil and gas operators a secure way to move critical OT data one-way to IT networks, historians, SIEM platforms, or the cloud—without increasing cyber risk to production environments. This keeps leadership informed, supports compliance reporting, and enables better operational decisions while protecting the systems that generate revenue.
Owl data diodes use a paired-card design: one card can only send data, and the other can only receive. This hardware-enforced, one-way architecture creates a true “air gap,” preventing data leakage, blocking malware from reaching OT networks, and reducing the likelihood of costly downtime or safety incidents.
Built to Meet Oil and Gas Cyber Security Regulations
Built to satisfy NRC, NERC CIP, and NIST expectations
Oil and gas operators face strict expectations around the cybersecurity technologies they deploy, requiring solutions that both meet regulatory mandates and deliver the highest level of protection to avoid operational and safety impacts. Regulatory frameworks such as NRC, NERC CIP, and NIST drive the need for robust, defensible controls that can withstand scrutiny from auditors, regulators, and insurers.
Owl protocol-filtering data diodes align to these regulatory controls and are widely recognized as a best practice for securing OT environments while still enabling safe data sharing. By enforcing one-way data flow and protocol-aware inspection, they help organizations demonstrate compliance, reduce regulatory and financial risk, and maintain continuous, compliant operations.
NRC
NRC: Regulatory Guide 5.71 – C.3.2.1 Security Defensive Architecture
NERC-CIP
NERC CIP-003-7: Attachment 1, Section 3.1
NERC CIP-005-6: R1 – Electronic Security Perimeter
NERC CIP-005-6: R2 – Remote Access Management
NERC-CIP-007-6: R1 – Ports and Services
NERC-CIP-007-6: R2 – Patch Management
NERC-CIP-007-6: R3 – Malicious Code Prevention
NERC-CIP-007-6: R4 – Security Event Monitoring
NERC-CIP-007-6: R5 – System Access Control
NERC-CIP-010-2: R2 – Configuration Monitoring
NIST
NIST 800-82, rev.2 – 5.1: Boundary Protection
NIST 800-82, rev.2 – 5.11: Unidirectional Gateways
