Secure AI Data Transfer Across Security Domains
Owl Cyber Defense Cross Domain Solutions (CDS) are foundational to secure, trusted AI containment & deployment across mission-critical networks. Purpose-built for the Department of Defense and Intelligence Community, Owl enables high-assurance data transfer across classified and disconnected environments, ensuring AI systems can access and move data securely while maintaining strict compliance and operational integrity in high-threat, bandwidth-constrained conditions.
Get Started
AI Containment & Probabilistic Systems
Scott Orton, CEO of Owl Cyber Defense, highlighted the concept of AI containment, a framework for managing probabilistic AI within deterministic legal and compliance structures. The challenges, he noted, lie not in the technology alone but in determining who sets the rules, who enforces them, and how organizations can adopt frameworks without impeding innovation. For Orton, success will be measured when agencies and enterprises are able to reap the benefits of AI-generated strategies while maintaining compliance with established frameworks.

Contain or be contained: The security imperative of controlling autonomous AI
Three trends are converging: the hyper-acceleration of security operations, the necessary removal of humans from the tactical loop, and the clash between probabilistic AI and our deterministic legal frameworks. The path forward is not to halt progress, but to embrace a new security model: AI containment.


The Doc Ock Problem: Securing AI Command from the Edge Inward
As we move toward an “agentic” force, a system where smaller AI models operate at the edge, lateral poisoning must be prevented. If one agent, like a remote image classification agent on a camera, is compromised, hardware must ensure the infection does not spread. Consider the analogy of the Spider-Man villain Doc Ock, whose mechanical arms were controlled by a neural interface. In the story, the inhibitor chip protecting his brain was destroyed, allowing the artificial intelligence in the arms to “talk back” and eventually corrupt his mind. In a military context, we face the same risk if our sensors are allowed to influence our central command. By using hardware data diodes to enforce quantum immune one-way flows, we ensure that edge devices can report data without the risk of an adversary pivoting from a compromised sensor to take over the central command-and-control “brain.”
–Michael Blake Technical Fellow Owl Cyber Defense
Assured AI Integrity for Defense & Intelligence
Owl Cyber Defense’s Cross Domain Solutions (CDS) enable trusted, resilient AI and data operations for U.S. national security. Owl delivers zero trust and hardware-enforced assurance, even across high-threat, bandwidth-limited, and multi-domain environments. Key benefits include:
- Enables secure, multi-level data transfers
- Maintains mission assurance under cyber threats
- Enforces zero trust: always verify, never assume
- Resilient, auditable performance in critical missions
- Trusted by DoD and intelligence community

One Portfolio. Every Boundary.
Hardware-Enforced + Protocol Aware: Owl Protocol Filtering Diodes
Hardware-enforced, one-way data flow from OT to IT — with FPGA-based protocol filtering that blocks anything non-compliant by design.
Assured Transfer for Critical Data: Owl Cross Domain Solutions
Realize NCDSMO-validated transfer of real-time data, voice, and video across classification boundaries — point-to-point or multi-domain. Built for high-assurance programs that need certified, policy-enforced boundary crossings without the risk and overhead of manual transfer processes.
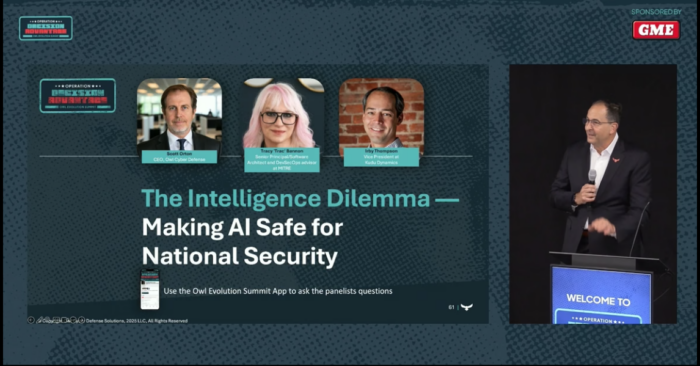
The Intelligence Dilemma: Making AI Safe for National Security
As artificial intelligence moves from concept to mission-critical reality, every organization faces the challenge of not just adopting AI, but containing its impact.
While AI delivers speed, scale, and strategic advantage, it also reshapes risk—introducing new vulnerabilities at machine-speed. Whether used in the field or the boardroom, unmanaged AI now threatens not just technical infrastructure but national security and public trust itself. The future belongs to those who secure AI with guardrails, accountability, and pragmatic governance—making safety a discipline, not just a debate.
2026 Predictions: What's Now, What's Next, What's Urgent
The podcast tackles the accelerating collapse of content trust in a world of deepfakes, AI-generated media, and short-form misinformation. As generative tools become indistinguishable from reality, they predict a sharp shift toward deep identity assurance powered by behavioral biometrics, cryptographic validation, and provable content provenance. In a future where “guaranteed human” becomes a competitive advantage, digital identity won’t be optional. It will be foundational.

Ready to take the next step in securing your networks?
Not sure which solution fits your use case?
We’re here to help you find the solution that best meets your needs. Provide us with as much detail as you can, and we’ll take it from there.
You can also reach us by phone at +1 (410) 290-1411